Austin Hacker Gives Security Spending Wish List for Local Businesses
Posted on 11/29/2022 by Charles Henderson

-

Charles Henderson
Global Managing Partner and Head of IBM Security X-Force
I lead a team of hackers who spend their days trying to figure out how to hack into the biggest companies and government agencies in the world. Let me start with some bad news. There is always a way in. Always. I am an optimist though, so there is some good news, too. Our years of hacking have given us a view into the biggest weaknesses of both government and the private sector, and there is still time to fix them.
In Texas, we’ve seen many of these weaknesses exploited in attacks on our state and local governments like the 2019 attack on 22 Texas cities. This was so grave that Governor Abbott declared the state’s first ever “Cyber Disaster.” If we don’t invest properly in security, it’s likely we will see more cyber disasters than natural disasters in our future.
Cybersecurity has been intertwined in the fabric of our future economic stability for some time. Smaller companies, cities and states are a soft target for attackers due to their size, often distributed nature, outdated IT systems, skills shortage, and lack of budget and negotiating power to hire top talent. A major challenge is the distributed nature of data which makes it easier for attackers to find gaps.
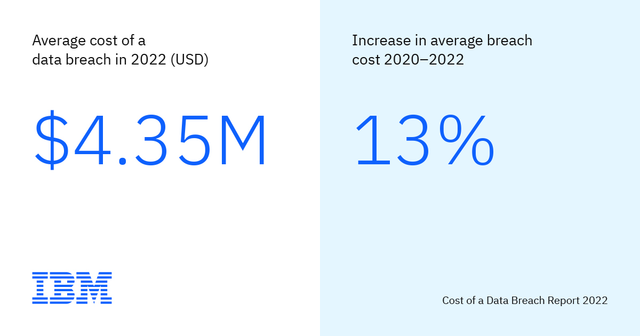
Costs associated with breaches are also rising. Our 2022 Cost of a Data Breach report found that data breach costs increased nearly 13% since 2020 and hit an all-time high of $4.35 million per incident. Yet, while breach costs keep growing, nearly half of all U.S. states still do not have a cybersecurity budget line item, according to a recent study conducted by The Harris Poll.
Training is one of the first areas I’d suggest Austin organizations prioritize their spending around. Appropriately training employees is one simple, yet significant, way to mitigate the cost of a data breach. The right training can help decrease per-breach costs by an average of $247,758, according to data from our latest Cost of a Data Breach report. Training might seem like an obvious area to invest in, but the right training is essential. Austin businesses should continue to focus on training employees on how to respond to incidents.
Austin businesses’ most trusted relationships may be their Achilles heel. Whether they be business partners or third-party applications that local businesses depend on to effectively operate, organizations in Austin, like all organizations, need to shift to a Zero Trust mindset when it comes to security. That means establishing a “default distrust” that automatically and iteratively corroborates that anything and anyone within its environment is legitimate. I’m not advocating to allocate spending to boxed “Zero Trust” solutions – because there are none. This is not a one and done action, but a culture shift every organization needs to embrace, and it’s a shift that will require scrutinizing trusted relationships and data access privileges, through intuitive security and policy controls.
Another growing concern is the massive number of software vulnerabilities that remain unpatched. There are hundreds of thousands of known vulnerabilities today at cybercriminals’ disposal to exploit for access into organizations’ environments. Considering the legacy systems and outdated IT that some organizations rely on, patching vulnerabilities must be a priority. Believe me when I say adversaries have locked their eyes on them.
Creating and acting out incident response plans must be a priority. It’s not a matter of if an organization’s incident response plan will be put to the test by a threat actor anymore, but a matter of when. Texas already has a documented cyber response plan, but it requires continuous investment to update and rehearse. All organizations need one. They need to know who their first responders are in the event of a cyberattack and what their attack playbook looks like. I’m talking about a set incident response plan that they are acutely familiar with and ready to activate. One that they’ve rehearsed to understand the pressure under which they’ll need to operate in a real-life scenario, but also who are the key stakeholders that need to be mobilized in the event of a cyberattack. This includes knowing where your most critical data lies, having back-ups offline and testing them too.
We share a collective responsibility as data stewards to collaborate and prevent cyberattacks that could devastate our organizations, our local economies, and our well-being. By fulfilling this “wish list,” Austin businesses can be much better positioned to keep malicious actors at bay and combat cybercrime more cohesively. Take it from a hacker who knows how cybercriminals think.
About the Author
Charles Henderson is Global Managing Partner and Head of IBM Security X-Force, based in Austin. With more than two decades of experience in the information security industry, Charles leads a global team of hackers, researchers, investigators and incident responders. The team provides clients - from Fortune 100 enterprise companies to small and mid-sized companies – offensive and defensive security services.
Related Categories: Membership